5 Stages of The Threat Intelligence Lifecycle
5 Stages of The Threat Intelligence Lifecycle
The cyber threat intelligence lifecycle is the process security teams use to build that preparedness. It is a structured, repeatable cycle that collects raw security data, refines it, and turns it into findings that drive real decisions. Organizations that follow it consistently are faster to detect threats, faster to respond, and better positioned to prevent damage.
Each Stage of the Threat Intelligence Lifecycle
|
This guide covers all five stages of the cyber threat intelligence lifecycle, what happens at each stage, and why the order and structure matter.
What Is the Threat Intelligence Lifecycle?
The threat intelligence lifecycle is a continuous process that transforms raw security data into actionable intelligence. It gives security teams the context they need to detect, analyze, and respond to threats before damage occurs.
It is also referred to as the cyber threat intelligence lifecycle or the threat intelligence cycle. Regardless of the term used, the purpose is the same: move from reactive defense to proactive prevention.
At its core, the lifecycle answers three questions:
- What threats exist?
- How do they affect the organization?
- What actions should be taken?
Organizations that skip this structure stay vulnerable. Those that follow it build a security program that gets sharper with every cycle.
What are The 5 Stages of the Cyber Threat Intelligence Lifecycle?
The cyber threat intelligence lifecycle consists of five interconnected stages that form a continuous loop.
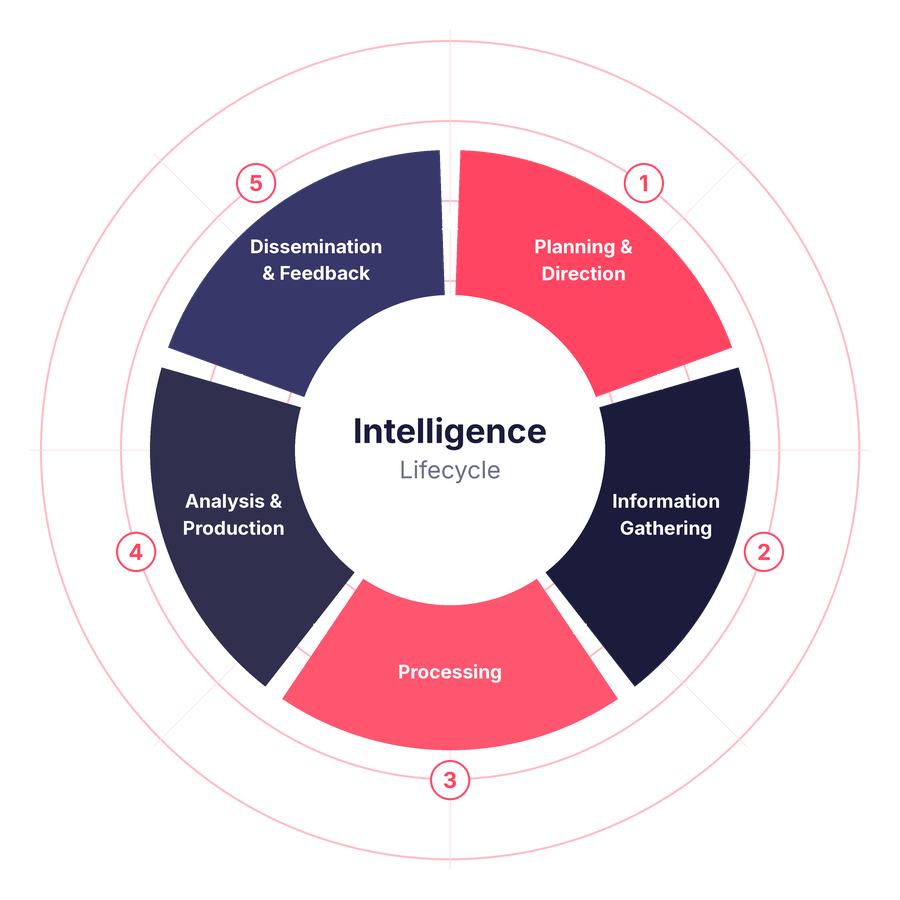
The five stages of the cyber threat intelligence lifecycle
Stage 1: Planning and Direction
Every CTI operation starts with a clear question: what do we actually need to know?
Without a clear answer, collection becomes scattered. Analysis becomes guesswork. And the finished intelligence product misses the mark entirely.
The planning and direction stage is where organizations define their intelligence requirements. This means identifying the specific threats they face, the assets they need to protect, and the questions they want the intelligence to answer.
It also means identifying the audience. A security analyst and a board member need very different outputs. Knowing who will read the finished intelligence shapes every decision that follows.
Key activities at this stage:
- Identify and prioritize critical assets
- Define the threat scenarios most relevant to the organization, such as phishing, ransomware, or APT activity
- Set clear objectives and KPIs for the intelligence program
- Determine who will consume the finished intelligence and in what format
Example: Your organization has seen a rise in phishing attempts over the past quarter. Before collecting any data, you need to define the right questions. How often are these attacks happening? Which employees or departments are being targeted? Have any attacks succeeded? Are other organizations in your sector seeing the same campaign?
These questions become your intelligence requirements. They guide collection, focus analysis, and determine what a useful finished product looks like.
Stage 2: Information Gathering (Collection)
With requirements in place, collection begins. This is where raw data comes in from a wide range of sources, both inside and outside the organization.
Internal sources include logs from firewalls, SIEM platforms, endpoint detection tools, and IDS/IPS systems. These give visibility into what is happening across your own environment.
External sources expand that picture significantly:
- OSINT: open-source intelligence from news sites, security blogs, and vendor advisories
- Deep and Dark Web forums where threat actors communicate and trade data
- Third-party threat intelligence feeds and commercial providers
- Industry ISACs (Information Sharing and Analysis Centers)
- Indicators of Compromise (IoCs) such as malicious IPs, file hashes, and phishing domains
- Government and sector specific threat advisories
- Threat research reports from security vendors and independent researchers
The volume of data at this stage will be large. That is expected. The goal is broad coverage. Later stages handle filtering and refinement.
The most important decision here is source selection. The right sources produce relevant, reliable data. Poor source selection creates gaps that weaken every stage that follows.
Stage 3: Processing
Raw data cannot be analyzed directly. It needs to be cleaned, organized, and structured into formats that analysts can work with. That is what the processing stage does.
Depending on what was collected, processing may involve:
- Removing duplicate and irrelevant data
- Normalizing formats such as STIX or JSON
- Tagging and organizing content with metadata
- Enriching data with additional context
- Decrypting protected content
- Translating foreign-language material
This stage can be done manually, but the volume of modern threat data makes full manual processing impractical for most teams. Many organizations use Threat Intelligence Platforms (TIPs) to automate large portions of this work. A semi-automated approach, combining machine processing with human review, tends to produce the best results.
Processing quality directly determines analysis quality. Clean, well-structured data leads to accurate findings. Poorly processed data leads to missed threats and wasted effort.
Stage 4: Analysis and Production
This is where processed data becomes intelligence.
The analysis stage takes structured data and turns it into findings that explain what happened, who was responsible, and what the organization should do next. It answers the core question of every CTI operation: why did this event occur, and what does it mean for us?
Analysts look for patterns, attribute activity to known threat actors where possible, and assess the level of risk to the organization. They map findings to established frameworks like MITRE ATT&CK or the Cyber Kill Chain to give context and structure to their conclusions.
Key outputs from this stage include:
- Indicators of compromise (IoCs)
- Identified threat patterns and attacker behaviors
- Attack techniques mapped to MITRE ATT&CK
- Risk assessments and recommended actions
The production part of this stage is the finished intelligence output. This might be a written report, a threat briefing, a dashboard, or an IoC feed, depending on the audience and the use case.
A few principles apply across all formats. Stay objective. Analysis must be based on evidence. Match the format to the audience. Technical teams need IoC lists and attack technique mappings. Executive stakeholders need risk summaries and recommended actions in plain language. Always include a course of action. Intelligence that describes a threat without recommending a response leaves the audience without direction.
Stage 5: Dissemination and Feedback
The intelligence is ready. Now it needs to reach the right people.
Dissemination is the process of delivering finished intelligence to its intended audience through secure channels. Getting it right requires care.
Different stakeholders need different products:
- SOC teams receive alerts and IoC feeds
- Security analysts receive technical reports and attack technique breakdowns
- Executives receive risk summaries and business impact assessments
Sending the wrong product to the wrong audience creates confusion and slows response. Timeliness matters too. Intelligence delivered late loses its value.
The second part of this stage is feedback. After receiving the intelligence, stakeholders assess whether it answered their original questions and met the requirements set in Stage 1. That assessment flows back into the next planning cycle.
Feedback is what makes the lifecycle improve over time. It closes the loop between intelligence consumers and intelligence producers. Each cycle becomes more focused, more relevant, and more useful than the one before.
Why the Threat Intelligence Lifecycle Matters
Without a defined process, threat intelligence becomes noise. Analysts spend time chasing alerts that go nowhere. Decisions get made without context. Response slows down.
A well-run threat intelligence lifecycle changes that. Key benefits include:
- Better threat detection accuracy
- Faster mean time to detect (MTTD) and mean time to respond (MTTR)
- Fewer false positives and less alert fatigue
- A proactive security posture instead of a reactive one
- Security decisions that align with actual business risk
Key Outputs of the Threat Intelligence Lifecycle
A well-run cyber threat intelligence lifecycle produces outputs that security teams can act on directly. These include:
- Indicators of compromise (IoCs)
- Threat intelligence reports tailored to each audience
- Risk assessments tied to business priorities
- Contextual threat insights that explain attacker intent and methods
- Automated response triggers integrated with SIEM, SOAR, and EDR tools
These outputs improve detection speed, reduce response time, and give decision-makers the context they need to act with confidence.
Common Challenges in the Threat Intelligence Lifecycle
Even mature organizations run into obstacles. Knowing the common ones helps you plan around them.
Data overload: The volume of available threat data is enormous. Without strong processing and filtering, teams end up buried in noise instead of acting on real threats.
Poor data quality: Irrelevant or outdated intelligence wastes analyst time and can lead to bad decisions. Source selection and regular source review are critical.
Lack of context: IoCs without explanation are not enough. An IP address flagged as malicious means little without context about who is using it and why.
Integration gaps: Disconnected tools create blind spots. Intelligence needs to flow into the platforms teams already use, such as SIEM, SOAR, and EDR systems.
Skill shortages: Experienced CTI analysts are in short supply. Automation and well-structured platforms help teams do more with less.
Best Practices for an Effective Threat Intelligence Lifecycle
These practices separate programs that produce real value from those that generate reports no one reads.
Define clear intelligence requirements: Focus on threats that are actually relevant to your organization. Broad collection without direction wastes resources.
Use multiple data sources: Combine internal telemetry with external feeds, OSINT, Dark Web monitoring, and industry sharing groups. No single source gives the full picture.
Automate processing and analysis where possible: AI and machine learning help teams handle data at scale without sacrificing accuracy.
Integrate intelligence with security tools: Intelligence that lives in a separate report has limited impact. Feed it directly into SIEM, SOAR, and EDR platforms so teams can act on it immediately.
Treat feedback as a required step: Feedback is not optional. It is what turns a one-time process into a continuously improving capability.
How to Implement the Cyber Threat Intelligence Lifecycle
A practical implementation follows these steps:
- Identify your critical assets and the threats most likely to target them
- Integrate diverse data sources covering internal logs, external feeds, and Dark Web monitoring
- Build or adopt data processing pipelines that normalize and enrich incoming data
- Apply analysis frameworks such as MITRE ATT&CK to structure findings consistently
- Deliver intelligence to stakeholders in formats suited to their role and technical level
- Collect feedback after each cycle and use it to sharpen the next round of requirements
Start simple. A focused, well-executed program covering a narrow set of requirements produces more value than a broad program with no clear direction.
Measuring the Effectiveness of the Threat Intelligence Lifecycle
Tracking the right metrics shows whether the lifecycle is delivering value and where to improve. Key KPIs include:
- Mean Time to Detect (MTTD): How long it takes to identify a threat after it appears
- Mean Time to Respond (MTTR): How long it takes to contain or neutralize a threat after detection
- False Positive Rate: The share of alerts that turn out to be non-threats
- Intelligence Utilization Rate: How often finished intelligence is actually used to make decisions or trigger responses
Consistent improvement across these metrics is the clearest sign that the lifecycle is working.
Why the Threat Intelligence Lifecycle Must Be Iterative
A single pass through the lifecycle produces useful intelligence. One pass is not enough.
Threat actors change tactics. New vulnerabilities emerge. Organizational risk shifts as systems, personnel, and operations evolve. An intelligence program that runs once and stops quickly falls out of sync with the real threat environment.
Running the cycle continuously, and letting each iteration build on feedback from the last, builds a capability that grows more accurate and more relevant over time. Requirements get sharper. Collection gets more targeted. Analysis gets faster. Finished products get more actionable.
That compounding improvement is what separates mature CTI programs from reactive ones.
SOCRadar’s Free Cyber Threat Intelligence
Most organizations struggle not with finding threat data, but with making sense of it. Feeds pile up. Alerts multiply. Analysts spend hours triaging noise instead of acting on real threats.
SOCRadar addresses this at every stage of the threat intelligence lifecycle. It pulls data from a continuously updated set of sources, applies AI-driven analysis to structure and prioritize findings, and delivers outputs that security teams can act on right away.
Key capabilities include:
- Dark Web Monitoring to detect stolen credentials, leaked data, and criminal activity targeting your organization
- Attack Surface Management to map your external exposure before attackers find it
- Brand Protection to catch phishing domains, impersonation attempts, and fraudulent use of your brand
- IoC Radar to enrich and investigate indicators of compromise in real time
- Threat Actor Tracking to follow the groups most likely to target your industry
SOCRadar also offers a free tier, giving security teams access to Dark Web reports, IoC lookups, breach checks, and SOC tools without a paid subscription. It is a practical starting point for organizations building a CTI capability from the ground up.
Frequently Asked Questions About the Cyber Threat Intelligence Lifecycle
What is the threat intelligence lifecycle? It is a structured, continuous process that converts raw security data into actionable intelligence. Security teams use it to detect, analyze, and respond to threats more effectively.
How many stages are in the threat intelligence lifecycle? Most frameworks describe five or six stages. The core stages are planning and direction, collection, processing, analysis and production, and dissemination and feedback.
What is the difference between the threat intelligence lifecycle and the threat intelligence process? The lifecycle is the full end-to-end framework, covering strategy through execution. The process refers to the operational steps taken within that framework. Both terms are often used interchangeably.
Why is the cyber threat intelligence lifecycle important? It moves organizations from reactive defense to proactive prevention. It improves detection speed, reduces response time, cuts false positives, and aligns security decisions with real business risk.
What is the first step in the threat intelligence lifecycle? Planning and direction. This stage defines intelligence requirements, identifies critical assets, and determines who will use the finished intelligence. Without this foundation, the rest of the cycle loses focus.
What are indicators of compromise (IoCs)? IoCs are pieces of evidence that suggest a system may have been compromised. Common examples include malicious IP addresses, suspicious file hashes, and known phishing domains. They are a core output of the analysis stage.
What is a Threat Intelligence Platform (TIP)? A TIP automates the collection, processing, and management of threat data. It helps teams handle large data volumes without relying entirely on manual review, and integrates with tools like SIEM and SOAR.
What is the difference between tactical and strategic threat intelligence? Tactical intelligence is technical. It covers specific threats, attack methods, and IoCs aimed at security analysts. Strategic intelligence is higher-level, focusing on trends, risk, and business impact for executives and decision-makers.
How does MITRE ATT&CK fit into the lifecycle? MITRE ATT&CK is a framework that maps adversary behaviors and techniques. CTI teams use it during the analysis stage to structure findings, identify defensive gaps, and communicate threats in a consistent, standardized way.
Can small organizations run a threat intelligence program? Yes. The lifecycle scales to any organization. Smaller teams can rely on third-party feeds, automated platforms, and free tools rather than building in-house collection and analysis from scratch. SOCRadar’s free tier is a practical starting point.
What happens after dissemination? Stakeholders review the intelligence, assess whether it met their requirements, and submit feedback. That feedback defines the objectives for the next cycle, making each iteration more targeted than the last.
What KPIs measure the success of a threat intelligence program? The most useful metrics are Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), false positive rate, and intelligence utilization rate. Consistent improvement across these signals that the program is working.
Security
via SOCRadar® Cyber Intelligence Inc. https://socradar.io
April 28, 2026 at 01:50PM
Cem Sarı
